Think of a technology risk management framework as the blueprint for your company's digital resilience. It’s not a dusty binder of rules, but a living, strategic plan for how you find, measure, and handle technology-related risks. It’s about making sure your tech choices support your business goals, not accidentally open the door to new threats.
Understanding the Blueprint for Digital Resilience
The best way to picture a technology risk management framework is to think about how a skyscraper is built. Before a single piece of steel is put in place, architects and engineers have already planned for everything—from gale-force winds to seismic shifts. They don't wait for a crisis to see if the building holds up; they design resilience right into its core.
A solid framework does the same for your technology. It gives you a consistent, repeatable process for managing the entire life of a risk, from the moment you spot it to the ongoing checks that keep it under control. This way, your business can keep moving forward without getting knocked off course by issues that could have been prevented.
Why Is This Framework So Critical Right Now?
Let's be honest: putting out fires as they pop up just doesn't work anymore. The old, reactive approach to tech problems is a recipe for disaster when your entire operation depends on digital systems to function.
A few big shifts are making this more urgent than ever:
- The Pace of Change: Companies are leaning on technology more than ever. Every cloud migration, new remote work policy, and interconnected system widens the potential field for something to go wrong.
- The AI Revolution: Bringing AI and machine learning into the fold creates entirely new kinds of risk. We're talking about everything from biased algorithms and poisoned data to models that simply stop working correctly. A framework gives you a way to handle these new, complex threats.
- Constant Cyber Threats: The bad guys are getting smarter and more persistent. A good framework helps you move from just defending yourself to being truly prepared and resilient.
A proactive framework is absolutely essential for steady growth, keeping the lights on, and earning trust. It stops being a "cost of doing business" and becomes a real strategic advantage that protects what you've built.
A Growing Market Signals a Growing Need
You don't have to take our word for it—just look at the numbers. The global risk management market hit a value of USD 14.9 billion in 2024. It’s expected to grow by 15% every year between 2025 and 2034.
This isn't just a random spike. It’s a direct response to how complicated business has become and how sophisticated cyber threats now are. For any leader, this trend is a clear signal: it’s time to get serious about modernizing how you handle technology risk.
Here’s a look at how the thinking has shifted from a simple compliance checklist to a driver of business value.
Core Tenets of a Modern Technology Risk Management Framework
| Principle | Traditional Approach (Compliance-Focused) | Modern Approach (Value-Driven) |
|---|---|---|
| Primary Goal | Pass audits and meet regulatory requirements. | Protect and enhance business value and enable innovation. |
| Risk View | Seen as a technical problem or a cost to be minimized. | Understood as a business issue tied to strategic objectives. |
| Scope | Focused on specific IT systems and infrastructure silos. | Holistic view across the entire organization and its ecosystem. |
| Process | Reactive; primarily responding to incidents and audit findings. | Proactive and predictive; continuously identifying and assessing risks. |
| Ownership | Belongs to the IT or security department. | Shared responsibility across all business units and leadership. |
| Outcome | A clean audit report and a list of checked boxes. | Improved decision-making, operational resilience, and competitive edge. |
This shift from a compliance-first mindset to a value-driven one is what separates companies that merely survive from those that thrive in the face of uncertainty.
A partner with real-world experience is key to navigating this. At Dr3amsystems, we help businesses accelerate outcomes by building and maintaining these frameworks from the ground up. Our end-to-end services cover everything from initial strategy to ongoing managed support, ensuring security and resilience are baked into every AI-driven solution and secure cloud migration. Backed by executive testimonials, we turn risk from a threat into a managed part of your growth plan.
The Core Components of an Effective Framework

A solid technology risk management framework isn't some single, dusty policy document. It’s actually built on four interconnected pillars that create a living cycle of finding, analyzing, fixing, and reviewing risks. Each piece has a specific job, and together, they turn risk management from a chaotic guessing game into a smart, strategic discipline.
You can think of these components like the stages of a check-up for your company's tech. First, you have to identify the symptoms (Risk Identification). Then, a specialist diagnoses how serious they are (Risk Assessment). Next, they create a treatment plan (Risk Mitigation). And finally, they schedule follow-ups to make sure the treatment is working (Risk Monitoring).
Let's dig into what each of these pillars really means in practice.
Risk Identification: Uncovering What You Don't Know
You can’t manage a risk you don't know exists. It’s as simple as that. This first stage is all about proactively hunting for potential threats before they turn into expensive, headline-grabbing incidents. It requires a systematic search for vulnerabilities across your entire technology ecosystem, from that aging server in the back room to the complex algorithms driving your new AI model.
Real identification goes far beyond just scanning for malware. You have to consider a whole spectrum of potential problems:
- Cybersecurity Vulnerabilities: The classic weak spots in your network, software, or cloud setups that attackers love to find.
- Operational Failures: The chance that a critical system just stops working, whether it's due to hardware failure, a nasty software bug, or simple human error.
- AI and Data Risks: This is a big one now. We're talking about everything from hidden bias in machine learning models to data privacy breaches or even "data poisoning" that skews your results.
- Compliance Gaps: Falling out of step with industry regulations, which can bring hefty fines and do serious damage to your reputation.
For instance, our Dr3am Security team at Dr3amsystems runs penetration tests and vulnerability assessments specifically to find these hidden weak points. In the same way, our Dr3am AI experts dive deep into machine learning models to root out potential bias, making sure your AI tools are both powerful and fair.
A common mistake is treating risk identification like a one-off project. New tech and evolving threats pop up constantly, so this has to be a continuous process of discovery that’s woven into the fabric of your operations.
Risk Assessment and Analysis: Prioritizing What Matters Most
Once you have a list of potential risks, what’s next? You need to figure out which ones actually matter. Not all risks are created equal. Risk assessment is the process of sizing up each threat you’ve found based on two key factors: its likelihood of happening and the potential impact it would have on the business if it did.
This analysis is what helps you move from a long, overwhelming list of worries to a clear, prioritized action plan. A risk with a low impact that’s highly unlikely to happen can be pushed down the list. But a high-impact risk with even a moderate chance of occurring? That needs immediate attention. This scoring process, often visualized in a risk matrix, brings clarity and helps you put your time and money where they'll do the most good.
Risk Mitigation and Control: Taking Action to Reduce Exposure
With a clear set of priorities, you can finally start designing and implementing controls to tackle them. Risk mitigation is all about taking deliberate steps to either lower the odds of a threat happening or soften the blow if it does. These actions, or "controls," usually fall into one of three buckets:
- Preventive Controls: These are proactive measures meant to stop an incident before it even starts. Think firewalls, strict access controls, and security awareness training for your team.
- Detective Controls: These are your alarm systems. They are designed to spot an incident while it's in progress or right after it has happened, like intrusion detection systems or security monitoring alerts.
- Corrective Controls: When something does go wrong, these are the steps you take to limit the damage and get back to business. Data backup and recovery plans are a classic example.
This is where a partner like Dr3amsystems can be invaluable. Our Dr3am Cloud team, for example, builds resilient, high-availability architectures that act as a powerful preventive control against downtime. These secure cloud migrations are designed from day one to mitigate the risks that come with legacy systems. You can learn more about our philosophy on building a strong defense in our guide to enterprise-grade security solutions.
Risk Monitoring and Reporting: Maintaining Constant Vigilance
Finally, a risk management framework isn't something you can "set and forget." The threat landscape changes daily. That’s why continuous monitoring and reporting are absolutely essential for making sure your controls are still working and for giving leadership a clear, current picture of the company's risk posture.
This involves setting up Key Risk Indicators (KRIs)—specific, measurable metrics that act as early warning signals. These KRIs are often tracked on real-time dashboards that give stakeholders the info they need to make smart, timely decisions. Regular, clear reporting keeps everyone on the same page and proves that risk management isn't just a binder on a shelf—it's an active, ongoing priority.
Navigating Key Frameworks Like NIST, ISO 31000, and COSO
Choosing a technology risk management framework can feel like trying to order from a menu where everything is written in code. With acronyms like NIST, ISO, and COSO flying around, it’s easy to get lost. The secret is knowing they aren't just competing instruction manuals—they're different tools for different jobs.
Think of it like picking a navigation app. One might give you meticulous, turn-by-turn directions for a dense city (that’s NIST). Another offers a high-level world map showing major routes and principles of travel (ISO 31000). A third is built for a logistics company, tying your travel plans directly to financial and operational results (COSO).
The goal isn't just to pick one. It’s to understand which tool, or combination of tools, fits your business journey. Making the right choice is the first step in turning a framework from a document on a shelf into a living, breathing part of your company's DNA.
NIST: The Technical and Security Go-To
For many U.S. organizations, particularly those laser-focused on tough cybersecurity and tech controls, the National Institute of Standards and Technology (NIST) frameworks are the gold standard. They are incredibly practical, handing your technical teams detailed controls and best practices they can implement right away.
The NIST Cybersecurity Framework (CSF) is famous for its five core functions: Identify, Protect, Detect, Respond, and Recover. It gives everyone a clear, actionable language for managing cyber threats. More recently, NIST has tackled the unique challenges of artificial intelligence.
Released on January 26, 2023, the NIST AI Risk Management Framework is a huge step forward in technology risk governance. Developed through collaboration between the private and public sectors, it’s quickly becoming essential for anyone building governance over AI systems. Among the most widely adopted frameworks globally, ISO 31000, NIST, and COSO dominate, and understanding them is critical for any leader implementing AI-driven solutions. You can learn more about the groundbreaking NIST AI framework and its role in responsible innovation.
ISO 31000: The Universal Guide for Enterprise-Wide Risk
While NIST often zooms in on the technical nuts and bolts, ISO 31000 zooms out. It provides a universal, principle-based approach to risk. Think of it less like a detailed checklist and more like a strategic guide for weaving risk management into every corner of the business, from the boardroom to the front lines.
ISO 31000 is built on a simple idea: risk management should create and protect value. Its key strengths are:
- Universality: It works for any organization, no matter its size, industry, or location.
- Integration: It pushes you to make risk management a core part of decision-making, not some siloed activity.
- Flexibility: It offers guiding principles instead of rigid rules, so you can tailor the framework to your specific reality.
This makes it a fantastic choice for companies that want to build a holistic, top-down risk culture.
COSO: Connecting Technology Risk to Business Performance
The Committee of Sponsoring Organizations of the Treadway Commission (COSO) framework traditionally speaks the language of finance, audit, and enterprise-level governance. Its main job is to connect all types of risk—including technology risk—back to the company’s financial reporting, operational efficiency, and strategic goals.
For a CEO or CFO, COSO is the framework that translates a technical vulnerability into business impact. It answers the crucial question: "How does this technology risk affect our bottom line, our compliance, and our ability to hit our targets?"
Choosing COSO, or integrating its principles, is the right move when the primary goal is to align your tech risk program with broader enterprise risk management (ERM) efforts and keep auditors and regulators happy.
Choosing and Implementing the Right Mix
The truth is, most organizations don't just pick one. They benefit from a hybrid approach, borrowing elements from each framework to build a solution that truly fits. This is where having a strategic partner makes all the difference.
At Dr3amsystems, we help you navigate this complex landscape. Our Dr3am IT experts start with a free consultation to get to know your unique business goals, regulatory pressures, and overall risk appetite.
From there, we help you select, customize, and implement the right framework components, making sure they’re practical and drive real results. Whether it's implementing NIST controls for a secure cloud migration or using ISO principles to foster a risk-aware culture, our hands-on execution ensures your technology risk management framework becomes a true strategic asset. You can explore our approach to strategic IT services and how they integrate risk management.
A Practical Roadmap for Implementing Your Framework
So, you're sold on the idea of a technology risk management framework. That's the easy part. The real challenge is moving it from a concept on a whiteboard to a living, breathing part of your business operations. Without a clear plan, even the most well-intentioned efforts can fizzle out, leaving you with nothing more than a dusty policy document.
Let's walk through a practical roadmap for turning theory into action. Think of this as a journey, not a sprint. Each phase builds on the one before it, creating a solid foundation for long-term resilience and continuous improvement.
Phase 1: Secure Executive Buy-In and Define Scope
Before you write a single policy or configure any tools, your first and most critical step is getting the leadership team on board. A framework that lacks executive sponsorship is, frankly, dead on arrival.
To get that crucial buy-in, you have to speak their language. Translate abstract technology risks into tangible business impacts. How does this affect revenue? What's the potential damage to our reputation? How does it align with our strategic goals? This is where a partner can make all the difference. Our initial free consultation at Dr3amsystems is designed to help you build that exact business case. We work with you to craft a clear roadmap that ties the framework's scope directly to measurable business value, making it an easy "yes" for the C-suite.
Phase 2: Assemble a Cross-Functional Team
Technology risk isn't just an "IT problem"—it’s a business-wide problem. The team you build to tackle it needs to reflect that reality. Pull in representatives from IT and security, of course, but don't forget legal, finance, and operations.
Bringing these different perspectives to the table is essential. It ensures the framework addresses risks across the entire organization and, just as importantly, creates a sense of shared ownership. This group will be the engine driving the initiative forward, making key decisions, and keeping the rest of the company in the loop.
Phase 3: Assess Your Current State and Identify Gaps
You can't plan a route to your destination if you don't know where you're starting from. This phase is all about taking an honest, thorough look at your existing technology, processes, and controls. The goal is to create an accurate inventory of your current risk posture.
From there, you can identify the biggest gaps between where you are today and where your chosen framework says you need to be. This assessment often uncovers hidden vulnerabilities, especially in older legacy systems or manual processes. The Dr3amsystems team excels at this discovery work, quickly finding opportunities for automation and pinpointing critical areas for modernization that will give you the biggest bang for your buck.
Phase 4: Select and Customize Your Framework
Armed with a clear understanding of your needs and gaps, you're ready to select and tailor the right framework. As we've discussed, options like NIST, ISO 31000, and COSO all have their strengths. The trick isn't to just pick one and adopt it wholesale. The real value comes from customizing it to fit your company's specific industry, size, and risk appetite.
In fact, the most effective strategies often blend elements from multiple frameworks.
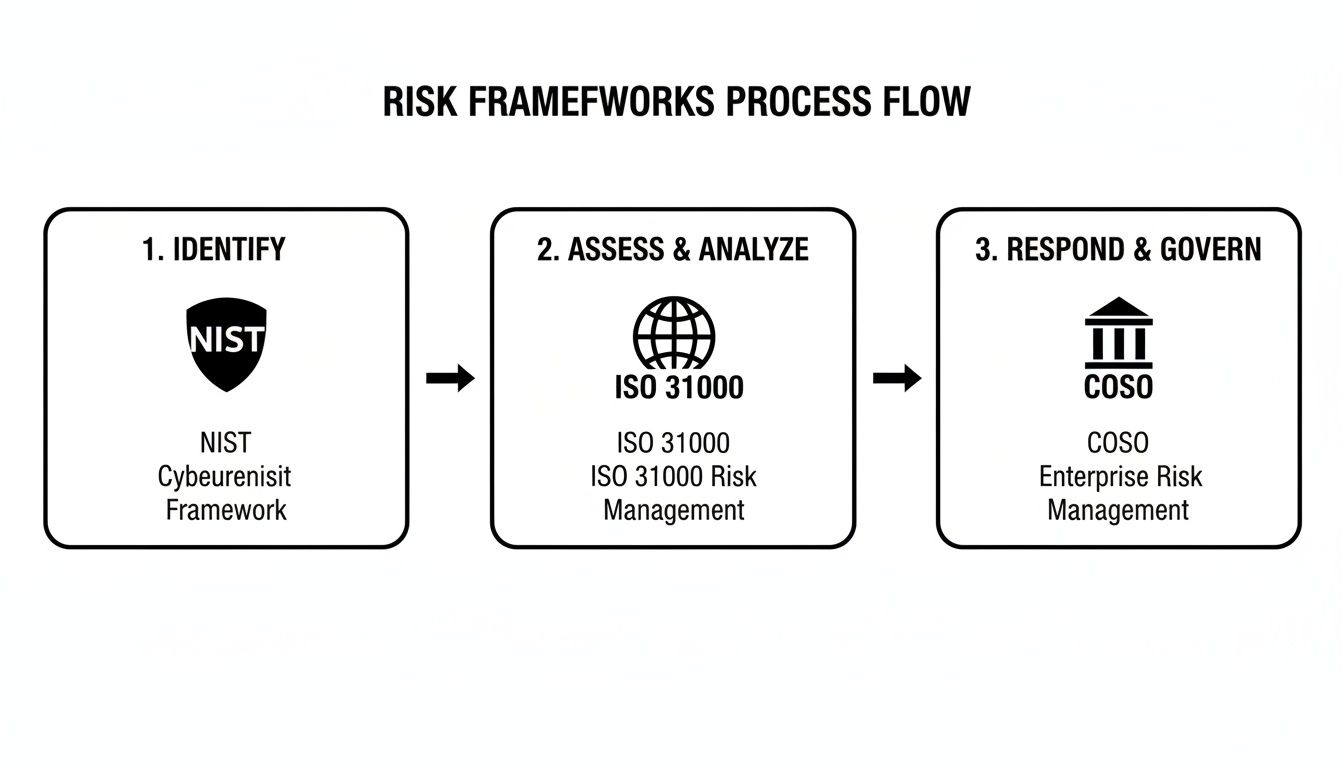
This diagram shows how a hybrid approach works beautifully. You can use NIST for its detailed technical identification, layer on ISO for assessment and analysis, and then use COSO for high-level governance. Together, they create a powerful, end-to-end strategy.
Phase 5: Develop and Maintain Your Framework
This is where the rubber really meets the road. Now it's time to develop and implement controls, set up monitoring systems, train your team, and establish a cycle of continuous improvement. These are the ongoing, operational tasks that require dedicated expertise and resources.
This long-term maintenance is where many internal teams get bogged down. A framework that isn't actively managed and updated quickly becomes obsolete.
An unmaintained risk framework is worse than having no framework at all. It creates a false sense of security while real threats evolve and multiply, leaving your organization exposed.
This is precisely why an ongoing partnership is so critical. Dr3amsystems' dedicated managed support and implementation services are built to handle these vital later stages. Our teams don't just help you implement controls correctly; we ensure they are continuously monitored, updated, and optimized. By managing this entire lifecycle for you, we deliver measurable results like 60% reductions in processing time and zero-downtime transitions, making sure your framework remains a powerful, living defense.
Applying the Framework to AI and Cloud Environments

A framework on paper is one thing, but its real power shows when you apply it to the messy, complicated world of modern technology. Two of the biggest game-changers for any business today are artificial intelligence and cloud computing—and both come with their own unique minefields.
A generic risk plan just won't cut it here. Applying your framework to these specific domains isn't about slowing down innovation. It’s about building the guardrails that let you push forward, faster and with more confidence, because you've already thought through the complex "what-ifs."
Taming the Unique Risks of Artificial Intelligence
AI isn't just another piece of software. Its risks are fundamentally different and can have ripple effects across your entire organization, touching everything from data integrity to brand reputation and legal compliance.
Without a solid governance plan, the very algorithms designed to give you a competitive edge can become a massive liability. You have to look beyond traditional IT security.
Here are a few of the big ones we see constantly:
- Algorithmic Bias: This is a classic "garbage in, garbage out" problem. If your AI model is trained on flawed or prejudiced data, it will produce discriminatory results. That's a fast track to reputational damage and legal headaches.
- Model Drift: The world changes, and so does data. An AI model that was perfectly accurate last year might start making terrible predictions today because its training is stale.
- Data Poisoning: Think of this as sabotage. A bad actor could intentionally feed corrupt data into your model’s training set, subtly manipulating its behavior for their own gain.
- Intellectual Property Leakage: Some sophisticated AI models can inadvertently reveal sensitive information from their training data. It’s a sneaky but severe security breach waiting to happen.
This is exactly where a technology risk management framework proves its worth. It forces you to establish specific controls for these AI threats, like building data validation pipelines to root out bias, setting up continuous monitoring to catch model drift early, and using fairness-aware algorithms.
This is where specialized expertise is non-negotiable. The team at Dr3am AI helps businesses adopt AI responsibly by implementing robust standards like the NIST AI RMF. We make sure your AI initiatives are not just powerful but also secure, fair, and aligned with your ethics. You can learn more about how Dr3amsystems delivers responsible AI-driven solutions.
Securing Your Journey to the Cloud
Moving to the cloud unlocks incredible scale and efficiency, but it also completely redraws the security map. It operates on a shared responsibility model, meaning your cloud provider secures the infrastructure, but you are responsible for securing whatever you build on it. A single, simple misconfiguration can expose your most sensitive data to the world.
Your framework needs to be adapted for this new reality. It gives you a systematic way to identify and plug the security holes that are unique to distributed, multi-tenant environments.
Common cloud risks we help clients navigate include:
- Cloud Misconfigurations: This is the low-hanging fruit for attackers. Simple errors in setup are a leading cause of data breaches, often leaving storage buckets or databases wide open.
- Insecure APIs: Your APIs are the front door to your cloud services. If they aren't properly secured, they offer a direct line for attackers to access your data and resources.
- Vendor Lock-In: Relying too heavily on a single provider's proprietary services can make it incredibly expensive and difficult to ever switch platforms or adopt a multi-cloud strategy down the road.
To make this more tangible, let's see how a framework applies specific controls to both AI and cloud risks side-by-side.
Technology Risk Management in Practice AI vs Cloud
This table offers a comparative look at specific risks and mitigation controls within AI and Cloud environments, demonstrating the framework's application.
| Risk Area | Example AI Risk | Example AI Control | Example Cloud Risk | Example Cloud Control |
|---|---|---|---|---|
| Data Integrity | An AI model is trained on biased data, leading to skewed predictions. | Implement a data validation pipeline that checks for and corrects bias before training. | A storage bucket containing customer data is accidentally made public. | Use a Cloud Security Posture Management (CSPM) tool to continuously scan for misconfigurations. |
| Operational Health | A machine learning model's accuracy degrades over time (model drift). | Set up automated monitoring with alerts that trigger when model performance drops. | An insecure API exposes sensitive backend services to the internet. | Enforce strong API authentication and authorization controls, combined with regular security testing. |
| Strategic | An AI system reveals proprietary information it learned from training data. | Use differential privacy techniques and data anonymization to protect sensitive information. | A multi-million dollar application is built entirely on one provider's proprietary services. | Adopt a multi-cloud strategy and use open-source or cloud-agnostic tools where possible. |
As you can see, the principles are the same, but the practical steps are tailored to the technology.
At Dr3amsystems, our Dr3am Cloud practice lives and breathes this kind of rigorous risk management. We build it into every stage of your cloud journey, from the initial strategy and secure migration to ongoing managed support. Our hands-on approach, which has delivered zero-downtime transitions for clients, ensures your cloud environment isn't just powerful—it's resilient and secure by design.
You Don't Have to Go It Alone: How Dr3amsystems Can Help
Let's be honest—managing technology risk is a massive undertaking. Between the breakneck pace of AI adoption, the complexities of securing the cloud, and the ever-present threat of a cyberattack, it’s far too much for any one team to handle. Building a solid risk management framework is non-negotiable, and bringing in the right partner is the smartest way to get it done right.
That’s where we come in. Dr3amsystems was built to be that expert partner, guiding you through every step of this journey. Our services are designed to line up perfectly with the essential parts of a high-performing risk framework.
A Unified Approach to Risk
We don't just offer piecemeal solutions; we provide a complete, integrated approach to securing your technology from the ground up. Our focused practices—Dr3am IT, Dr3am Cloud, Dr3am AI, Dr3am Security, Dr3am Hosting, and Dr3am Marketing—provide end-to-end services spanning strategy, implementation, and ongoing optimization.
- Dr3am AI & Dr3am Security: We tackle the most sophisticated threats head-on, helping you identify and shut down risks before they become problems.
- Dr3am Cloud & Dr3am IT: Our teams focus on building and maintaining resilient cloud infrastructure and operational controls that keep your business running smoothly.
- Dr3am Hosting: We provide the secure, stable foundation your critical systems need to perform reliably day in and day out.
This structure allows us to offer true end-to-end support, turning your risk management strategy into a practical reality. We always start with a free consultation to map out a clear plan that connects your technology investments directly to your business goals. From there, we roll up our sleeves and get to work, providing hands-on implementation and ongoing managed support to make sure your framework isn't just a document—it's a living, breathing part of your operations.
When you partner with an expert team, risk management stops being a reactive cost center and becomes a genuine strategic advantage. It gives you the confidence to innovate, knowing your technology is secure, reliable, and ready to scale.
Our clients have seen firsthand how well this works. We've helped businesses achieve 60% reductions in processing time and pull off zero-downtime migrations, proving that robust security and business growth can absolutely go hand-in-hand.
Working with an experienced team gives you more than just peace of mind; it delivers a sustainable competitive edge. You can learn more about how we deliver results by getting to know the Dr3amsystems team. Let's build a framework that not only protects your business today but also empowers it for whatever comes next.
Your Questions Answered: Practical Advice on Tech Risk Management
Getting a technology risk management framework off the ground always brings up practical questions. It's one thing to understand the theory, but another to put it into practice. Let's tackle some of the most common questions we hear from leaders who are ready to build a more resilient organization.
We Don’t Have a Huge Team or Budget. Where Do We Even Begin?
Starting small isn't a compromise; it's the smartest way forward. You don't need a massive team to make a real impact. The key is to focus your energy where it matters most.
Begin by identifying your crown jewels—the critical business processes that keep your company running. What technology underpins them? A quick, high-level risk assessment will help you zero in on the top three to five technology risks that could genuinely hurt your operations.
Forget about trying to implement a full-blown NIST or ISO framework on day one. Instead, prioritize the basics that give you the biggest bang for your buck: strong access controls, reliable data backups, and regular security training for your people. These foundational steps are the bedrock of any solid program.
This is exactly where an experienced partner can make all the difference. In a free consultation, our team at Dr3amsystems can help you pinpoint those high-impact areas and map out a plan that grows with you. It’s all about making sure every dollar you invest delivers immediate protection and real business value.
What’s the Real Difference Between a Technology Risk Framework and a Cybersecurity Framework?
This is a great question, and the answer comes down to scope. While they're definitely related, they aren't the same thing.
Think of a cybersecurity framework (like the NIST CSF) as your specialized security guard. It’s laser-focused on one critical job: protecting your digital assets from cyber threats, whether they come from outside hackers or internal mistakes. Its main goal is to stop data breaches, prevent unauthorized access, and fend off malicious attacks.
A technology risk management framework, on the other hand, has a much wider lens. It sees the bigger picture. It absolutely includes cybersecurity as a core component, but it also accounts for a whole range of other things that can go wrong with technology:
- Operational Failures: What happens if a server crashes or critical software has a bug?
- Project Disasters: How do you prevent a new tech implementation from going way over budget or failing completely?
- Outdated Tech: What’s the risk of relying on old systems that are no longer supported or reliable?
- New Tech Headaches: Are there hidden risks like bias in your AI models or a major outage from your cloud provider?
- Compliance Gaps: Are you meeting all the regulatory rules related to how you use technology?
The easiest way to remember it is this: all cybersecurity risks are technology risks, but not all technology risks are about cybersecurity.
How Often Should We Revisit Our Framework? Is It a “Set It and Forget It” Thing?
Definitely not! Your technology risk framework needs to be a living, breathing part of your operations, not a document that gathers dust on a shelf.
As a rule of thumb, you should conduct a full, formal review at least once a year. This is your chance to make sure the framework still aligns with your business goals and reflects the current threat environment.
But some events should trigger an immediate review. Think of these as wake-up calls: a major security incident, rolling out a game-changing technology like generative AI, or a big shift in your business or the regulations you have to follow.
Beyond formal reviews, continuous monitoring is essential for making smart adjustments on the fly. This is where Dr3amsystems’ managed support services really shine—we provide the ongoing oversight to ensure your framework stays effective as your business and the world keep changing.
Ready to build a technology risk management framework that doesn't just prevent problems but actually drives resilience and growth? Dr3amsystems offers the expert guidance and hands-on help to perfectly align your technology with your business goals.
Let's start the conversation with a free consultation and design a roadmap that delivers clear, measurable results.