Think of cybersecurity like securing your physical office. You wouldn't just leave the front door unlocked, would you? The same logic applies to your digital assets. Protecting your data, operations, and reputation isn't just an IT problem anymore—it's a core business function.
Cybersecurity solutions are the tools and practices, from firewalls to employee training, that protect your company from digital theft, damage, and snooping. In a world where a single breach can shut you down, these defenses are non-negotiable.
Building Your Digital Fortress

With so many of us working from home and relying on cloud services, the "attack surface" for every business has exploded. There are simply more doors for bad actors to try and open. This new reality requires a new mindset. We need to stop seeing security as just a defense against fear and start seeing it as a launchpad for innovation and growth.
From Cost Center to Strategic Advantage
Viewing security as nothing more than an expense is an old-school way of thinking that leaves you vulnerable. Today, smart businesses treat cybersecurity as a proactive strategy that helps them achieve their goals. The aim is to create a secure environment where your team can embrace new technology and innovate freely, without putting the company at risk.
This is where having the right technology partner changes everything. A firm like Dr3amsystems can help weave security directly into your business strategy. Their Dr3am Security practice, part of a comprehensive suite of services, is all about building resilient systems that don't just protect your data but also make your operations more efficient and set you up for long-term growth.
A strong security posture is a competitive advantage. It ensures business continuity, protects brand reputation, and builds the deep customer trust necessary for long-term success.
Responding to Modern Threats
The threats we face are always evolving. We're seeing sophisticated ransomware, AI-powered attacks, and a sharp rise in supply chain breaches that can cripple a business overnight. These aren't just hypotheticals; they're real-world risks that make solid security an absolute must for staying in business.
Cybercriminals are getting smarter, taking full advantage of the shift to remote work. Phishing attacks and other scams are increasingly targeting employees outside the traditional office perimeter.
By making security a cornerstone of your business strategy, you transform a potential weakness into a real strength. Expert guidance, like the dedicated managed support from Dr3amsystems' Dr3am IT services, keeps your critical systems running smoothly and securely, giving you the confidence to focus on what you do best: growing your business.
Navigating the Modern Threat Landscape

Before you can build a solid defense, you have to know what you're up against. The world of cyber threats can feel chaotic, but most attacks follow predictable patterns. The first step in creating effective cybersecurity solutions for businesses is getting familiar with the common playbook attackers use.
Think of your company’s network as a bustling city. Cybercriminals are always probing for unlocked doors, open windows, and distracted people. Their tactics range from simple street scams to elaborate, coordinated heists, but the goal is always the same: exploit a weakness for financial gain.
This constant pressure is why we're seeing huge investments in security. The global cybersecurity market is booming as companies scramble to protect their digital assets from a flood of increasingly clever attacks. This growth isn't just a trend; it's a direct response to criminals disrupting operations and stealing data, forcing businesses to shore up their defenses. You can dig into the market trends and drivers to see just how critical this has become.
The Anatomy of Common Cyberattacks
When you understand how an attack works, it stops being a mysterious force and becomes a problem you can solve. Four types of threats consistently cause the most headaches for businesses, big and small.
- Phishing: This is the modern version of a classic con. Attackers send emails that look like they're from a trusted source—a boss, a bank, a well-known vendor—to trick an employee into giving up a password or financial information. One persuasive email can completely bypass millions of dollars in security technology.
- Ransomware: Imagine a digital kidnapper holding your data hostage. This malicious software locks up all your critical files, grinding your business to a halt. The attackers then demand a hefty ransom, usually in cryptocurrency, to give you the key.
- Malware: This is a catch-all term for any hostile software, from viruses and spyware to trojans. Like a saboteur slipped behind enemy lines, malware can steal data silently over months, actively damage your systems, or give an attacker a secret back door into your network.
- Insider Threats: Sometimes the call is coming from inside the house. An insider threat could be a disgruntled employee looking to do harm, or it could be a well-intentioned staff member who makes a simple mistake, like emailing a sensitive file to the wrong person.
A multi-layered defense is essential because no single tool can stop every type of attack. Each layer, from email filters to endpoint protection, acts as another barrier, making it significantly harder for criminals to succeed.
From Theory to Reality
Let’s make this real. An accountant gets an email that looks like it’s from the CEO. It’s urgent—a wire transfer needs to be sent to a new vendor right now to close a big deal. The logo looks right, the tone feels familiar. Without a protocol to verify such requests, the accountant sends the money. It’s gone forever.
This is a classic social engineering attack, and it costs businesses millions every year.
This is where having a strategic partner like Dr3amsystems makes all the difference. Their Dr3am Security practice goes beyond just installing software. They help you build a resilient security culture, implement the right controls, and provide dedicated managed support to defend against these very real threats. Their pragmatic, results-focused approach means you can focus on running your business, not constantly looking over your shoulder.
The Essential Layers of Your Security Stack
Good cybersecurity isn’t about a single piece of software or a magic-bullet solution. It’s about building a “defense-in-depth” strategy, where multiple layers work together to protect your business.
Think of it like securing a medieval castle. You wouldn't just build a high wall. You’d also have a moat, guards at the gates, archers on the towers, and special protection for the crown jewels. If one defense fails, another is there to stop the threat. Your business needs the same layered approach for its digital assets.
This strategy is the foundation of modern cybersecurity solutions for businesses. Each component shores up a different potential weakness. Let's break down the essential layers of your digital castle.
Network Security: The Moat and Walls
Your network is the perimeter, the first line of defense separating your internal systems from the wild west of the public internet. Network security solutions are your moat and fortified walls, controlling every bit of traffic that tries to get in or out.
The cornerstone here is the firewall. A firewall acts as a digital gatekeeper, inspecting all incoming and outgoing data and blocking anything that doesn't follow the security rules you've set. Today’s firewalls are far more sophisticated, capable of spotting suspicious patterns and preventing intrusions before they ever reach your team.
Other crucial network tools include:
- Virtual Private Networks (VPNs): These create a secure, encrypted tunnel for remote employees to access company resources, essentially extending the castle walls to protect them wherever they work.
- Intrusion Detection and Prevention Systems (IDPS): Think of these as vigilant sentries patrolling the walls, actively scanning for signs of an attack and moving to block it immediately.
Endpoint Security: Guards at Every Gate
Even with a strong perimeter, you need guards protecting every door and window inside the castle. In your business, these entry points are your endpoints—the laptops, desktops, servers, and smartphones your team uses every single day.
Endpoint security is all about protecting these individual devices, which are often the main targets for phishing scams and malware. An endpoint protection platform (EPP) is like assigning an elite guard to each device, combining several functions:
- Antivirus & Anti-malware: The basics—scanning for and eliminating known malicious software.
- Behavioral Analysis: This is more advanced. It watches for unusual activity on a device that could signal a compromise, even from a brand-new, never-before-seen threat.
- Device Control: Manages who can plug in USB drives or other peripherals, preventing malware injection or data theft.
With remote work becoming the norm, securing every endpoint has become non-negotiable. A single compromised laptop at a coffee shop can become a gateway into your entire corporate network.
Cloud Security: Protecting Assets Beyond the Walls
Let’s face it, many of your most valuable assets aren't even inside the castle anymore. They’re stored in the cloud—in platforms like AWS, Microsoft 365, or Google Workspace.
Securing these assets requires a different mindset. You're operating under a shared responsibility model: the cloud provider secures their infrastructure (the "cloud" itself), but you are responsible for securing your data and controlling who can access it within that cloud. A misconfigured cloud service is like leaving a treasure chest unguarded in a public square.
This is where a technology partner with deep expertise in both cloud and security is so important. For example, Dr3amsystems' Dr3am Security and Dr3am Cloud practices are designed to work hand-in-hand. They ensure that as you migrate to the cloud, your security actually gets stronger, providing secure, zero-downtime transitions and ongoing management so you can leverage the cloud confidently.
Data Security: Protecting the Crown Jewels
At the very heart of your business is the real treasure: your data. We're talking about customer information, financial records, and intellectual property. Data security is the final, most crucial layer, focused on protecting the information itself, no matter where it lives or who is trying to access it.
Key data security measures include:
- Encryption: Scrambling your data so it’s completely unreadable without the right decryption key.
- Data Loss Prevention (DLP): These tools act as a final checkpoint, identifying and blocking sensitive data from being emailed or transferred out of the company without authorization.
- Access Control: This is about enforcing the principle of least privilege—making sure people can only see or touch the data they absolutely need to do their jobs.
To give you a clearer picture, here’s a quick summary of how these pieces fit together.
Key Cybersecurity Solution Categories at a Glance
| Solution Category | Primary Function | Key Assets Protected |
|---|---|---|
| Network Security | Controls traffic at the perimeter, blocking external threats. | Company network, servers, internal systems. |
| Endpoint Security | Secures individual devices where users work. | Laptops, desktops, mobile phones, servers. |
| Cloud Security | Protects data and applications hosted in the cloud. | Cloud storage, SaaS apps (e.g., M365), IaaS/PaaS. |
| Data Security | Protects the information itself through encryption and access control. | Customer data, financial records, intellectual property. |
By layering these solutions, you build a security posture that is resilient, comprehensive, and far stronger than any single tool could ever be.
To learn more about building a defensive strategy that fits your unique business needs, see how our expert-led security services can help fortify your operations against modern threats.
From Reactive Defense to Proactive Security Operations
Having strong walls and vigilant guards is essential, but the best security strategies don’t just block attacks they see coming—they actively hunt for threats before they can do any real damage. This is the crucial shift from a reactive defense to proactive security operations.
Think of it this way: locking your doors at night is reactive. Having a 24/7 surveillance team actively monitoring for suspicious behavior around your entire property? That's proactive.
This shift isn't just a "nice-to-have" anymore. As businesses move more operations to the cloud, the demand for smarter security is skyrocketing. Global spending on cybersecurity is set to grow substantially, with North America leading the charge thanks to persistent threats and tough compliance rules. A deep dive into the cybersecurity market growth makes it clear why being proactive is the new standard.
This diagram shows how foundational security layers—network, endpoint, and cloud—work together to form a complete defense.
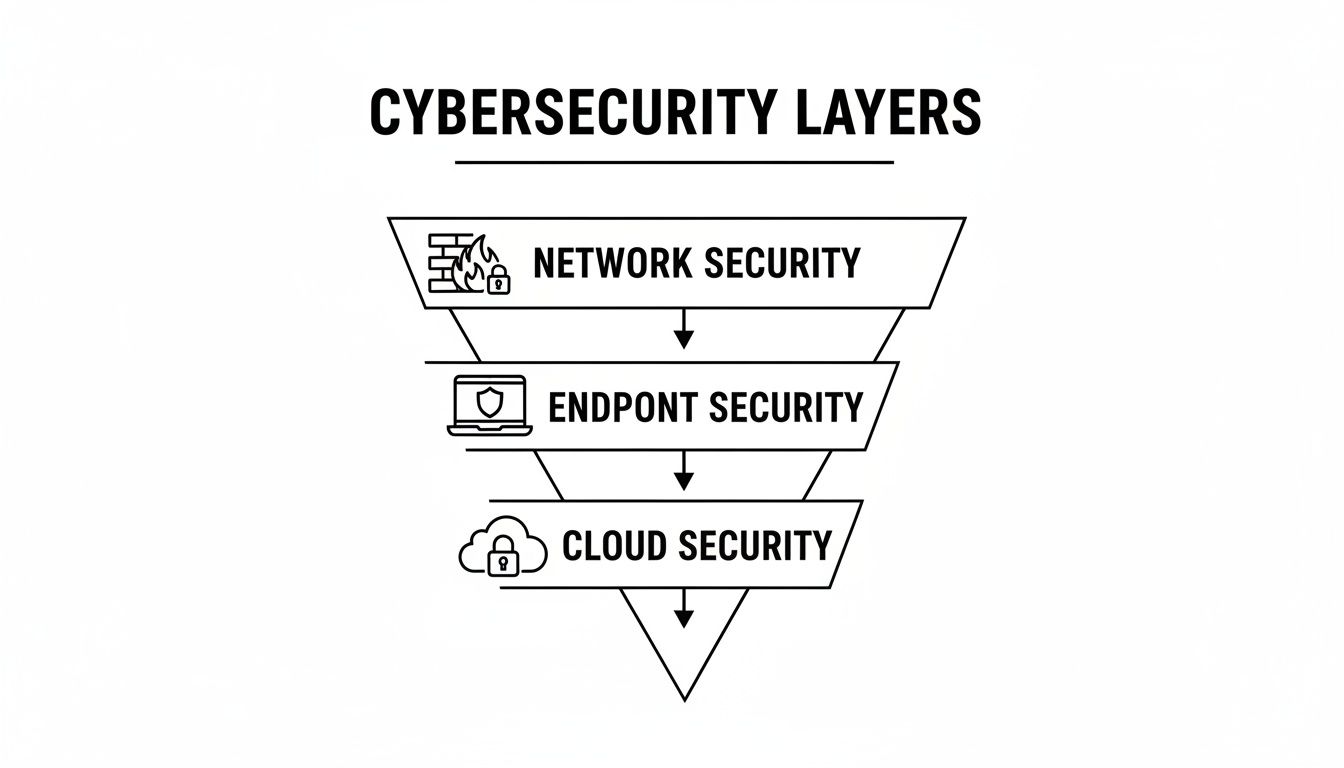
Each layer plugs a specific hole, but the real power comes from an integrated strategy where all your defenses work in concert to protect what matters most.
Unifying Your Defenses with SIEM and XDR
To get that all-important bird's-eye view of your entire digital footprint, you need a central command center. This is where tools like Security Information and Event Management (SIEM) and Extended Detection and Response (XDR) come in. They’re the brains of your security operation, pulling in data from all your other tools to see the bigger picture.
Imagine your firewall, endpoint protection, and cloud security tools are all sending you separate reports. A SIEM platform gathers every single one of these reports in one place. It then uses smart analysis to connect the dots, spotting patterns that would be completely invisible to any single tool. For instance, it could correlate a strange login attempt on a server in one country with an unusual file download on a laptop in another, flagging a potential coordinated attack.
XDR takes this a step further. It doesn't just centralize the data; it enriches it with more context and helps automate the response, allowing security teams to investigate and shut down threats much faster.
Think of SIEM and XDR as your company's security nervous system. They collect signals from every corner of your organization, process them in real-time, and alert you to the pain points before serious damage is done.
The Power of Managed Detection and Response
Let's be realistic: building an in-house Security Operations Center (SOC) to run these advanced tools 24/7 is a massive undertaking. It means hiring a team of highly specialized—and very expensive—analysts and keeping them on duty around the clock. For most businesses, that’s just not practical.
This is where Managed Detection and Response (MDR) services come to the rescue. An MDR provider is essentially your outsourced SOC. You get access to an elite team of security experts and top-tier technology for a fraction of what it would cost to build it yourself. They handle the heavy lifting of monitoring, threat hunting, and incident response so your team can stay focused on running the business.
This approach offers some serious advantages:
- 24/7/365 Monitoring: Cybercriminals don't work 9-to-5. MDR ensures an expert is always watching over your systems.
- Proactive Threat Hunting: Instead of just waiting for an alarm to go off, MDR teams actively search for hidden threats inside your network.
- Rapid Incident Response: When a threat is found, the MDR team acts immediately to contain and neutralize it, minimizing the potential fallout.
Working with a technology partner like Dr3amsystems puts this level of protection within reach. Through their Dr3am Security practice and dedicated managed support, you gain the peace of mind that comes from having a results-focused team monitoring your environment. This partnership ensures your critical operations run smoothly while elevating your security from reactive to truly proactive. This kind of robust security is also the perfect complement to other essential services, like the reliable and secure hosting infrastructure your business depends on.
Creating Your Strategic Cybersecurity Roadmap
Having a powerful suite of security tools is one thing, but without a clear plan, it's like having a pile of expensive building materials with no blueprint. The best cybersecurity solutions for businesses are always guided by a deliberate strategy. A roadmap is what turns your security investments from a scattered collection of products into a cohesive, goal-oriented defense system.
This plan acts as your north star. It ensures every decision, purchase, and policy moves you closer to a more secure and resilient state of operations. It gives you clarity, gets your team on the same page, and helps you put resources where they’ll actually make a difference.
Step 1: Assess Your Unique Risks
Before you can build effective defenses, you have to know what you're protecting and who you're protecting it from. Every business is different, with its own unique mix of critical assets, operational quirks, and potential weak spots.
The first move is a thorough risk assessment. This isn't just a technical audit; it's a real-world business analysis.
- Identify Critical Assets: What data, systems, and processes are absolutely essential for your business to function? Think customer databases, financial records, proprietary source code, or the software that runs your operations.
- Map Potential Threats: Based on your industry and business model, what are the most likely threats you'll face? A healthcare provider's biggest worry might be a breach of patient records, while a manufacturer might be more concerned about ransomware shutting down their production line.
- Analyze Vulnerabilities: Where are the weak points? This could be anything from unpatched software and a lack of employee training on phishing to misconfigured cloud services.
Step 2: Define Clear Security Goals
Once you have a clear picture of your risks, you can set meaningful security goals. These shouldn't be vague statements like "improve security." They need to be specific, measurable, and tied directly to the risks you just identified.
For example, a solid goal would be: "Reduce the risk of a successful phishing attack by 50% within six months through a combination of advanced email filtering and mandatory employee training." That kind of clarity turns your strategy from an abstract idea into an actionable project with a real finish line.
A well-defined roadmap aligns technology with business value. The objective isn't just to buy security tools; it's to strengthen operations, protect revenue, and enable confident growth.
Step 3: Prioritize Investments and Implementation
You can't fix everything at once—and you shouldn't try. A strategic roadmap helps you prioritize your investments for maximum impact. Start with the solutions that address your most significant risks first. This approach ensures your budget is spent wisely, tackling the most dangerous vulnerabilities before you move on to less critical areas.
This is where having a technology partner like Dr3amsystems can be invaluable. Their process often begins with a free consultation designed specifically to clarify your goals and build a practical roadmap. They specialize in aligning technology with business outcomes, ensuring every step—from strengthening security to executing a secure cloud migration—is purposeful and delivers a measurable return. That kind of expert guidance helps turn a strategic vision into a well-executed reality.
Connecting Security Investment to Business Growth
It's easy to look at cybersecurity as just another unavoidable cost, a line item on the budget that doesn't generate revenue. But that's a shortsighted and dangerous view. Smart leaders have flipped the script, recognizing that security isn't a cost center at all—it's a critical enabler of growth, stability, and trust.
Strong cybersecurity solutions for businesses aren't just about stopping bad things from happening. They're about creating a secure, stable foundation that allows the good things—innovation, expansion, and customer relationships—to thrive.
When your systems are locked down, your business keeps running, no matter what. That’s the core of business continuity. A single ransomware attack can freeze your operations, shatter your supply chain, and shut down your revenue stream for days or even weeks. Proactive security prevents this chaos, ensuring you stay online and continue to serve your customers.
From Defense to a Competitive Advantage
Beyond simply keeping the lights on, a rock-solid security posture gives you a serious edge over the competition. In a world where data breaches are front-page news, customers are paying close attention. They're actively choosing to work with companies they trust to keep their information safe.
This trust isn't just a feeling; it translates directly into tangible business value.
- Protecting Brand Reputation: It can take years to build a great reputation and only one data breach to destroy it. Strong security is your best brand insurance.
- Ensuring Regulatory Compliance: Meeting standards like GDPR, HIPAA, or CCPA is more than a legal checkbox. It signals to everyone that you take data ethics seriously, which builds tremendous confidence.
- Building Customer Trust: When people feel their data is safe with you, they stick around. They buy more, and they tell their friends. That's loyalty in action.
"A strong security posture is not an expense. It's an investment in resilience, reputation, and revenue. By protecting the business, you enable it to grow confidently and capture new opportunities."
Measuring the Return on Security Investment
So, how do you know if the investment is paying off? You have to measure it. The real ROI of security goes far beyond simply counting how many attacks you blocked. It’s about tracking real-world business outcomes.
Think about the massive costs you avoided: crippling compliance fines, sky-high incident response bills, and lost revenue from downtime. It's also about the efficiency you gain when your teams aren't constantly putting out fires.
This is where working with a results-oriented partner makes all the difference. When a firm can point to zero-downtime transitions during a complex migration or show measurable results like a 60% reduction in processing time, they're providing proof of value. By implementing the right enterprise-grade solutions, an expert partner like Dr3amsystems helps protect your assets while actively boosting your bottom line. Suddenly, security becomes one of the smartest investments you can make.
Frequently Asked Questions About Business Cybersecurity
It's natural to have questions when you're navigating the world of business cybersecurity. Getting clear, straightforward answers is the first step toward making smart investments that actually protect your company and help it grow.
My Business Is Small. Do I Really Need All This?
Yes, absolutely. It's a common misconception that cybercriminals only go after the big fish. In reality, they often see smaller businesses as softer targets, assuming they have weaker defenses. For a growing company, a single security breach can be devastating, both financially and to your reputation.
The goal isn't to buy a massive, enterprise-grade security stack on day one. It's about being strategic. A good technology partner, like Dr3amsystems, can help you build a security plan that fits your specific risks and budget, starting with the essentials and scaling up as your business expands.
How Much Should We Budget for Cybersecurity?
You'll often hear benchmarks suggesting you set aside 7-15% of your IT budget for security, but that's just a starting point. A much smarter way to approach it is by starting with a thorough risk assessment. This process helps you figure out what your most valuable assets are and where your biggest weak spots are.
Once you know what’s most important to protect, you can invest your money where it will have the greatest impact. At Dr3amsystems, we walk clients through this exact process, starting with a free consultation to map out a plan that focuses your budget on what truly matters.
What’s the Single Most Important First Step We Can Take?
While the right technology is critical, the single most impactful first step you can take is building a security-aware culture through ongoing employee training. Your team is your first line of defense. They’re the ones who will spot the phishing emails and social engineering tactics that are behind the vast majority of all security breaches.
When you pair solid technical controls with a sharp, vigilant team, you create a security posture that’s genuinely resilient. A well-trained employee can spot a threat that even the best software might miss, making them your most valuable security asset.
Ready to build a cybersecurity strategy that enables growth instead of holding it back? The experts at Dr3amsystems provide end-to-end services—from strategy and implementation to dedicated managed support—to fortify your business. Schedule a free consultation to design a roadmap that aligns technology with your business goals. Learn more at https://dr3amsystems.com.